The 4 Things You Need to Do Before Deleting an App
Updated: Mar. 20, 2024
Removing an app isn't as simple as it sounds.
It’s always a good idea to remove apps taking up precious space on your phone—especially ones that could be spying on you. But for some apps, you’ll need to do more than simply hit the “delete” button. While you may think you’ve dumped an app, its remnants could still be lurking in the background, leaving your device vulnerable or causing other issues.
“The biggest misconception is that once an app is deleted, the relationship with the app and the company that owns it is severed,” says Jean Vixamar, a senior vulnerability management specialist in Tampa, Florida. “That could not be further from the truth. Those terms and conditions you casually checked off matter. In most cases, you’ve given them unfettered permission to use your data in whatever ways they see fit, within the interpretation of applicable laws, of course.”
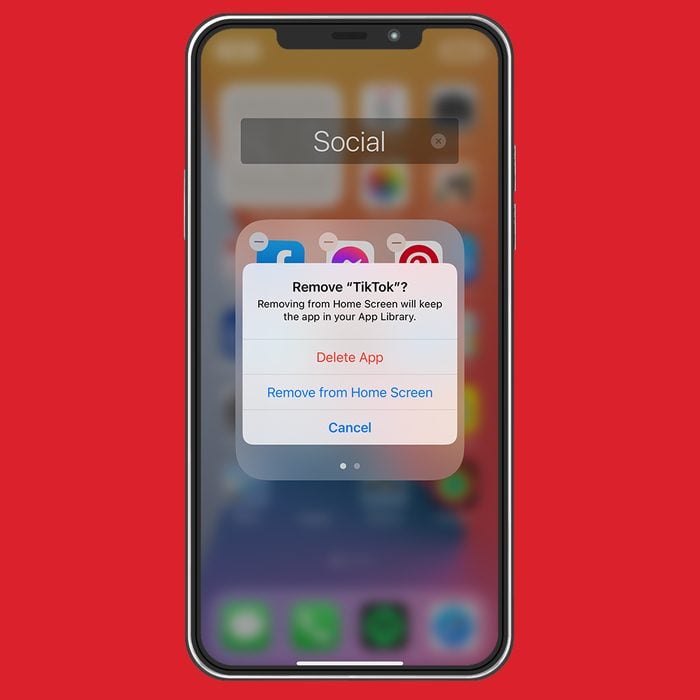
Luckily, there is a way to make sure that an app is fully gone—and that your personal information stays safe. Here’s what you need to know to protect your phone and data when deleting an app. To beef up your phone’s security even more, learn how to delete iPhone apps, how to hide apps on an iPhone, and how to check (and change) your iPhone privacy settings.
Convenience comes at a cost
Many of us regularly use a variety of apps throughout the day, implementing them automatically into our daily routines without giving them much thought. Without a doubt, they can make our lives easier and save us quite a bit of time. But this convenience can have a downside.
“Applications are everywhere,” says Steve Tcherchian, Chief Information Security Officer at XYPRO, a cybersecurity analytics company. “We use them to shop, bank, order dinner, get a ride, keep our house warm, and even keep track of our children. But our data needs to be shared with applications for them to provide value. In most cases, this means extremely sensitive information about us and our lives.”
Although we share our data with the hope that the app’s creator will keep it safe, that is not always the case. Many apps fail to use encryption and other security features, leaving our private information vulnerable to criminals and hackers. In fact, Tcherchian adds, apps are the top mode of attack in most data breaches, according to the 2021 version of Verizon’s Data Breach Investigation Report. FYI, that’s not the only reason you should be worried about smartphone apps stealing your data.
Why deleting apps can be tricky
Turns out, your data doesn’t magically disappear when you delete an app. Apps are often part of an intricate web of interconnected tools, products, and sites that track and share your information, likely without you even realizing it. “Think about a dating app, for example,” says Tcherchian. “Typically, these are linked through a Facebook account that enables the app to access pictures, friends lists, and other information about yourself available through Facebook. Assume the application developer, with your permission, has access to everything available through your Facebook profile.”
Tcherchian cautions app users not to assume that their private information will be protected. “Most applications are horribly insecure, and developers do not follow security best practices when developing an application,” he explains. “Applications are designed for functionality, not security. Security is difficult and time-consuming, often adding delays to product launch and revenue-generating activities. Assume that the application does not have your data properly secured.”
The right way to remove an app completely
There are multiple steps involved in making sure an app is fully disconnected from your phone and other accounts. James E. Lee, Chief Operating Officer at Identity Theft Resource Center, recommends following this process before deleting an app:
- First, delete all your data on the app. While the instructions for erasing data are different for each app, you can usually find an option to delete stored data under menu titles like “privacy,” “account settings,” or “security,” Lee says. From there, follow the prompts to remove account data or stored history on the app.
- You should also log in to your account through a web browser, if possible. Sometimes you’ll find additional settings available through the desktop version of the app. “Mobile apps are often skinny versions of a full-featured application you use on the web or your desktop,” Lee explains. “So, it’s a good idea to log into the app through a web browser to make sure you did not miss any additional settings that may not be available in mobile versions of an app.”
- Unlink or revoke any Facebook or Google integrations you may have enabled by going to the app’s settings tab, finding the “linked accounts” option, and removing the app or link you want to delete. You can also remove integrations through the linked account instead. Just sign in to the linked account, check your settings to see which apps they share data with, and then delete what you no longer use. Lee suggests going to the linked account for exact instructions and using their contact form or chat function if you have a question.
- If you can’t find any information about deleting your data on an app, Lee recommends contacting the app’s customer service team and requesting in writing that your data be completely deleted. For more mobile security tips, steal these secrets from people who never get hacked.
Apps you should avoid
Certain apps are especially troublesome. Experts recommend immediately deleting these apps that security experts would never have on their phones—or, better yet, not installing them in the first place. “There are a number of apps that are extremely dangerous from a security and privacy perspective,” says Vixamar. “You should be wary of any app that requires access to your photos, files, camera, microphone, and more—totally or in combination. You have to ask yourself, ‘Does this app really need all of this access, or do I really need this app?'” Before hitting the “download” button, watch out for these signs you shouldn’t trust an app, and in general, make sure you know how to tell if your phone has been hacked.
Sources:
- Steve Tcherchian, Chief Information Security Officer at XYPRO
- Jean Vixamar, senior vulnerability management specialist
- Verizon: 2021 Data Breach Investigations Report
- James E. Lee, Chief Operating Officer at Identity Theft Resource Center




